Android Marcher posing as Super Mario Run
Nintendo recently released the game Super Mario Run for iOS platform. Soon after the release, this game became a sensational hit on Apple iTunes store. However, this game’s Android version does not exist and there has been no official confirmation on the release. The attackers are taking advantage of the game’s popularity and spreading malware posing as Android version of Super Mario Run game.
We had written about a similar scam which occurred during the release of another popular Nintendo game – Pokemon GO. Recently, ThreatlabZ came across a variant of Android Marcher Trojan disguised as the Super Mario Run app in one of our threat feeds. This malware scams users by presenting fake finance apps and credit card page in order to harvest banking details.
Marcher history
Marcher is a sophisticated banking malware targeting wide variety of banking and financial apps and credit cards by presenting fake overlay pages. Once the user’s mobile device is infected, the malware waits for victims to open one of its targeted apps and then presents fake overlay page asking for banking details. Unsuspecting victims will provide the details that will be harvested and sent out to its command and control (C&C) server. We have seen this malware constantly evolve and take advantage of the recent trends in order to target a large number of users. We have covered similar campaigns in past related to Marcher malware here and here.
Technical Details
In this case, Marcher malware is disguising as Super Mario Run android app. Knowing that Android users are eagerly waiting for this game, the malware will attempt to present fake web page claiming the release of this game in Android version.
Following are the details of Malware:
- Name : Super Mario Run
- Package Name : uiq.pizfbwzbvxmtkmtbhnijdsrhdixqwd
- MD5 : d332560f1fc3e6dc58d94d6fa0dab748
- Detections : 12/55(at time of analysis)
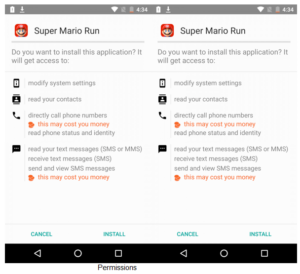
Upon installation, the malware asks for multiple permissions including administrative rights as seen below.
In previous variants of Marcher, we observed this malware family targeting well known Australian, UK, and French banks.
We have observed this variant targeting account management app along with well known banks. Here is a code snippet showing sample targeted apps:
![]()
Following is the full list of targeted apps by this variant:
- fr.lcl.android.customerarea – https://play.google.com/store/apps/details?id=fr.lcl.android.customerarea
- mobi.societegenerale.mobile.lappli – https://play.google.com/store/apps/details?id=mobi.societegenerale.mobile.lappli
- com.cic_prod.bad – https://play.google.com/store/apps/details?id=com.cic_prod.bad
- net.bnpparibas.mescomptes – https://play.google.com/store/apps/details?id=net.bnpparibas.mescomptes
- com.rbs.mobile.android.ubr – https://play.google.com/store/apps/details?id=com.rbs.mobile.android.ubr
- com.grppl.android.shell.halifax – https://play.google.com/store/apps/details?id=com.grppl.android.shell.halifax
- com.fullsix.android.labanquepostale.accountaccess – https://play.google.com/store/apps/details?id=com.fullsix.android.labanquepostale.accountaccess
- com.barclays.android.barclaysmobilebanking – https://play.google.com/store/apps/details?id=com.barclays.android.barclaysmobilebanking
- com.caisseepargne.android.mobilebanking – https://play.google.com/store/apps/details?id=com.caisseepargne.android.mobilebanking
- com.rbs.mobile.android.rbs – https://play.google.com/store/apps/details?id=com.rbs.mobile.android.rbs
- fr.banquepopulaire.cyberplus – https://play.google.com/store/apps/details?id=fr.banquepopulaire.cyberplus
- com.htsu.hsbcpersonalbanking – https://play.google.com/store/apps/details?id=com.htsu.hsbcpersonalbanking
- fr.creditagricole.androidapp – https://play.google.com/store/apps/details?id=fr.creditagricole.androidapp
- uk.co.tsb.mobilebank – https://play.google.com/store/apps/details?id=uk.co.tsb.mobilebank
- com.grppl.android.shell.CMBlloydsTSB73 – https://play.google.com/store/apps/details?id=com.grppl.android.shell.CMBlloydsTSB73
- com.grppl.android.shell.BOS – https://play.google.com/store/apps/details?id=com.grppl.android.shell.BOS
- com.rbs.mobile.android.natwest – https://play.google.com/store/apps/details?id=com.rbs.mobile.android.natwest
- uk.co.santander.santanderUK – https://play.google.com/store/apps/details?id=uk.co.santander.santanderUK
Like previous Marcher variants, this variant also presents fake credit card pages once an infected victim opens the Play Store. It locks out the Play Store until user supply the credit card information as seen below:
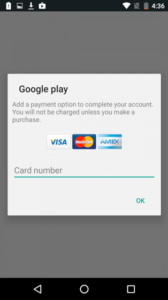
Fake credit card page
However, banking overlay pages served by the C&C were not functioning properly at the time of writing this blog. We are suspecting that the malware variant is still under development.
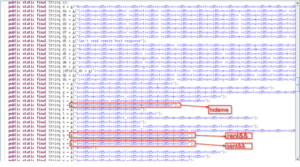
In this variant we have observed a new obfuscation technique as well, where all important string characters are delimited with ‘<<zB5>>‘ as seen below.
Below code snippet shows the hardcoded C&C location.

C&C location
Conclusion
Android Marcher has been around since 2013 and continues to actively target mobile user’s financial information. To avoid being a victim of such malware, it is always a good practice to download apps from trusted app stores such as Google Play. This can be enforced by unchecking the “Unknown Sources” option under the “Security” settings of your device.








