Throughout the conversations I have had this year, there has been one recurring theme – automation.
Hardly a new concept; I was writing about the benefits of automation over the past few years, but it seems that 2014 has brought this back to the forefront.
Look at the examples: Oxford University’s Sadie Creese said that we as humans “are good as spotting shapes and patterns”, but we automate as much as possible so we can focus on spaces.
On the contrary, Jeremiah Grossman, CEO of Whitehat Security, said that we have no choice but to automate, and said that it is a “false choice that we can automate things away” and challenged anyone to name something in software security or internet security that we have automated away, as we still need people. “I say automate more, but nothing will be automated away.”
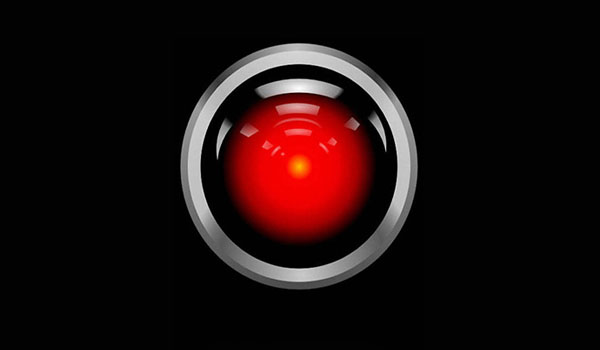
TK Keanini, Lancope CTO, said that he saw a successful future that is not Skynet, but machine to machine communication is tricky, and if we believe we will fix the human to computer automation, and IoT is talking to system, then that is tricky also.
“This machine has to authenticate with this machine, that credential can be stowed and there is no human involved and that practice has some Achilles heel as programmers get better at authenticating to other machines and give them appropriate authorisation, and not just the keys to the kingdom.”
Differing views, but no one really explaining why this trend is there. I caught up with Paul Nguyen, president of global security solutions at CSG Invotas, who talked earlier this year about the automation trend.
So why is this being talked about? Nguyen said that there are different paradigms and themes, and one is that the fight for talent is tough and as people quickly become seasoned security professionals, businesses cannot hire fast enough or keep the people there, so retention is an issue.
“They are looking at automation as a way to bridge the gap between the resource from where they are to where they need to be as a capability,” he said.
“I talked to one customer, and he could not hire any analysts, and while tier two people were valuable, he asked me if he could automate tier one to bridge the gap?”
Nguyen said that when you have a problem, you throw people at it, and automation is replacing manual tasks that people normally do. He explained that the rise of automation is a people and threat thing, as there is direct correlation between incidents going up and people not dealing with it, and the trajectory is so high that people cannot keep up.
“All it takes is one out of 5,000 alerts that could be the one, and you could be chasing one that is a more impactful targeted attack,” he said.
The other trend is around technology, and around incorporating it into suites.
Nguyen explained that companies buy assets in, and businesses like CSG Invotas create artificial interoperability as a piece of software becomes a hub to tie the spikes together, and orchestration component a big thing.
“Automation is the time acceleration component of the process, and the ability to unify,” he e
xplained.
“Think of the things you need to buy and the people you need to manage it. So just because you buy the latest and greatest, someone has got to manage it. So you can buy it and it is a small thing to do, but that is why automation is a trend, as what do you do when the attacks are going up and you cannot keep up?”
I asked Nguyen where he saw the future of this as a trend? He said that it is a combination of threats increasing, plus the lack of workforce to scale, and the complexity of the technology environment that we are dealing with.
He said: “The reality is, we are increasing the attack surface so we are making the problem larger, and then we throw the latest and greatest tools in to deal with it so you are compounding the security architecture, so those elements are the biggest pain points for customers and they cannot keep up and it is a never ending battle that they are losing now.”
We are the robots, welcome to the machine.