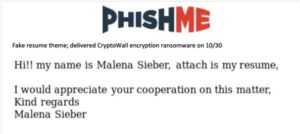
PhishMe’s Research Team has today warned of a phishing message circulating, supposedly from someone seeking employment. However, instead of just spelling mistakes or perhaps grammatical errors, the attachment is far more sinister as it contains Ransomware.
Ronnie Tokazowski – Senior Researcher at PhishMe explains, “Often November is a busy time for UK employers as graduates, returning from post-university summer breaks, start actively seeing employment. While the message itself is extremely vague, the fact that it has got through an organisation’s anti-virus protections could mean it’s deemed benign. However, its not, as the attachment actually unleashes Ransomware.”
Ronnie concludes, “Ransomware – malware that infects a system and encrypts the data, has proved exceptionally effective in recent months with many falling victim and paying vast sums in the hope of receiving the decryption keys – although they’re not always forthcoming. The best protection against this, and indeed any malware utilised in email attacks, is the effective use of threat intelligence to maintain situational awareness and rapidly identify threats that might impact an organisation as well as the effective training of end-users who are the intended targets of these email attacks.”








