A blockchain is a data structure, originally used by bitcoin, that maintains a growing list of transaction records in a way that is extremely resistant to tampering. This technology is seen by many as the basis for creating distributed ledgers for a wide range of applications. But what are the risks associated with the use of this technology?
Distributed ledgers offer a range of potential benefits to both private sector organizations as well as government and public services. They can be widely distributed and yet at the same time precisely controlled. They reduce costs by automating the processes involved in verifying and rapidly publishing authorized changes. They are structured in a way that makes it extremely difficult to change or tamper with existing authorized content. They can be the basis for new kinds of applications like smart contracts.
The benefits of distributed ledgers based on blockchain are that they provide assurance against three kinds of risks. These are illustrated in the figure below:
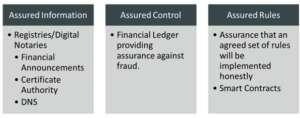
Figure 1: Kinds of Assurance from Distributed Ledgers.
However, every new technology is claimed to offer unparalleled benefits, many of which do not materialise in practice. Equally organizations that fail to exploit the new technologies may find to their cost that they have lost market. The constant challenge is to identify and quantify the real potential benefits and balance these against a realistic view of the potential risks.
A report from KuppingerCole, that is shortly to be published, identifies some of the potential risks that need to be considered by any organization considering the use of blockchain platforms. The mentioned report identifies 19 different risks and classifies these according to their likelihood and potential impact. These risks are categorized as being:
- Critical risks – with a high likelihood and a very high impact that have the potential to disrupt transaction processing or damage integrity.
- Important Risks – with a very high impact but a lower likelihood that could damage the business using the system.
- Risks needing consideration – some of these, like the long term durability of the cryptographic algorithms used, may not crystalize in the short term but could pose longer term problems.
The following figure illustrates an example of each of these risks.
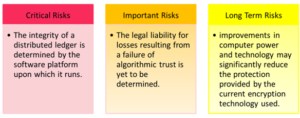
Figure 2: Examples of Risks
Blockchain based distributed ledgers are generating much hype and it is very difficult to recognize the real value and the real risks from emerging technologies. KuppingerCole recommends that organizations should put in place an action plan to:
- Identify the opportunities for the exploitation of blockchain technology.
- Quantify the expected benefits and potential risks from these.
- Choose an appropriate delivery architecture and platform.
- Recommend the actions needed to manage the risks identified based on the detailed recommendations in this document
KuppingerCole has already published research into this subject:
- Advisory Note: Demystifying the Blockchain – 71555 – KuppingerCole
- Advisory Note: Blockchain Impact on the Financial Industry – 71601 – KuppingerCole
To find out more on this subject attend the Blockchain Seminar in Munich on May 9th: Moving Beyond the Hype: EIC 2016 Blockchain Seminar – ID Conferences
Mike Small has been Senior Analyst at KuppingerCole since more than 4 years and mainly focusses on security and risk management in the Cloud. He is a member of the London Chapter of ISACA Security Advisory Group, a Chartered Engineer, a Chartered Information Technology Professional, a Fellow of the British Computer Society, and a Member of the Institution of Engineering and Technology. Mike Small has a first class honors degree in engineering from Brunel University. Until 2009, he worked for CA (now CA Technologies Inc.) where he developed the identity and access management strategy for distributed systems. This strategy led to the developments and acquisitions that contributed to CA‘s IAM product line. At KuppingerCole he covers the topics Cloud Provider Selection and Assurance, Information Security Program Maturity Assessments, Information Stewardship as well as Big Data.








