SecureWorks® Counter Threat Unit (CTU)® researchers have tracked the spread of several notorious ransomware families to the Asia-Pacific region, underscoring efforts by some attackers to localise their tools to target multiple geographies.
According to the CTU, the current top four ransomware families – Locky, Cerber, CryptXXX and TorrentLocker – are targeting computer users in Japan with localized versions of their threats. In addition, the threat actors behind CryptXXX have developed a localized version for South Korea as well.
“Unlike other types of malware that are mostly designed to compromise the system covertly, ransomware requires end-user interaction to achieve its goal – collecting ransom,” explained SecureWorks researcher You Nakatsuru. “This makes localizing the threat particularly useful to attackers.”
Localisation can take one or all of the following forms: attackers can write ransomware messages in the local language; strategically compromise local websites; deliver the ransomware via spam campaigns in the local language; or provide payment instruments using local bitcoin wallet and exchange market lists.
In Japan in particular, SecureWorks has noted a spike in ransomware infections starting in 2015. Before that, ransomware infections were not that common in the region because ransomware was primarily delivered via spam emails written in English. As a result, Japan-based computer users tended not to fall prey to the malicious emails. However, since 2015 there has been an uptick in ransomware in the area being distributed using exploit kits, and ransomware authors have started developing multi-language ransomware such as Locky.
The effort by cyber attackers to localise their weapons highlights the importance of information sharing and situational awareness, as a threat in one geographical region can soon become a threat in another. Below is a chart of when several ransomware families were initially spotted in the region by members of the security community. The dates noted in the table below are the first reported dates from each Asia-Pacific country’s national Computer Security Incident Response Team.
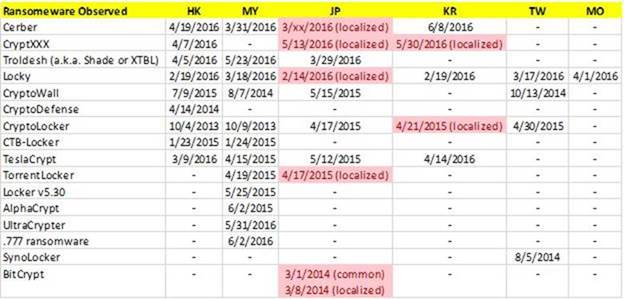
Table 1. Initial ransomware incident reported in each geographical area
| HK – Hong Kong, China MY – Malaysia JP – Japan KR – Republic of Korea (S. Korea) TW – Chinese Taipei (Taiwan) MO – Macao |
*pink cells with (localized) included are the dates on which a localised version variant were discovered. The exact Japan discovery date for Cerber is unknown, aside from it being discovered in March.
CTU researchers discovered that the Locky ransomware was being used by threat actors to target computer users in Asia-Pacific during Q12016, the very same time the ransomware was being used to infect victims in North America and EMEA, indicating that the threat actors were targeting multiple countries during the same timeframe.
Localisation can happen at different paces. For example, despite the English version of CryptXXX being reported in the region in April 2016, a localized version of the ransomware was not reported in Japan and South Korea until May 2016.
In contrast, the CTU team noted that it took nearly a year and a half for a localized version of CryptoLocker to be identified in South Korea after the English version was reported in Hong Kong. This localised version is believed to be the work of a different group. However, in the case of CryptXXX, CTU suspects that the localised variant that appeared in May is the work of the same threat actors using CryptXXX elsewhere in the region.
Any time gap between the discovery of threats in different regions offers an opportunity for other areas to proactively protect themselves against attacks. While “local” malware variants may use different infrastructures and network indicators, such as IPs and domains, countermeasures designed to detect/filter ransomware command and control (C2) packets will be still effective unless significant change in C2 protocol occurs.
Additional research findings
- “SecureWorks CTU has observed over four dozen distinct families of ransomware emerge since the beginning of 2015. The most prolific families can each be responsible for millions of spam emails, hundreds of thousands of infected systems, and millions of dollars in ransom payments. Generally , 0.25% to 3.0% of victims elect to pay a ransom to the attackers holding their data hostage. We ascertain the largest operations are making several million dollars per year and the annual losses from all ransomware families combined exceed $10 million annually. The cost of business disruption, lost data, and infection remediation due to ransomware likely extends into the hundreds of millions of dollars annually,” said Keith Jarvis, senior security researcher for SecureWorks’ Counter Threat Unit research team. Jarvis explains, “meaning attackers need to destroy data on anywhere from 30 to 400 computers for every victim who relents and pays the ransom.”
The top four ransomware families of August 2016 are:
- Locky—it is run by one single group who in turn utilizes two main affiliate groups to seed out the ransomware
- Cerber—The CTU saw Cerber emerge in February 2016, and the hackers who were using CryptoWall switch over to Cerber
- CryptXXX
- TorrentLocker—it is the elder statesman of the ransomware ecosystem and is run by a single hacker group.
The top ransomware families are being spread via malicious spam and exploit kits.
SecureWorks CTU researches saw high volumes of CryptXxx a commodity ransomware during June, 2016. CTU researchers observed ransom demands of 0.7, 1.2, or 2.4 BTC, with most victims receiving a demand for 1.2 BTC. CTU analysis revealed at least 69 victims who paid ransoms totaling more than 85.6 BTC (approximately $53,500) from June 6 to July 7, 2016.
In the first part of 2016, SecureWorks Security and Risk Consulting Team (SRC) and CTU Team saw the following APT-Style Ransomware Cases:
Case Study 1
A U.S. based technology company had 30% of their systems, within their network compromised, with the samsam ransomware. The initial intrusion started two months before the ransomware was deployed. The initial ransom demand, made by the attackers, was for 1.5 bitcoins per system or 22 bitcoins for all systems compromised within the network.
Case Study 2
A U.S. based manufacturing company was a victim of ransomware, and the initial access vector used to launch the ransomware was first compromised in 2013. The ransom demanded was again 1.5 bitcoins per system or 22 bitcoins for all systems.
Case Study 3
A transportation company had numerous systems compromised with samsam ransomware. The activity was uncovered when system administrators started losing their ability to remotely administer key servers in the network. The ransom demanded was 1 bitcoin per system.
Aspects of Tactics/Tools/Vulnerabilities Used in Ransomware Incidents, as monitored by Dell SecureWorks Incident Response Team and Special Ops CTU Team
- Infections are not occurring as a result of phishing, such as with Locky
- Access is being gained through vulnerabilities to older, unpatched, unmanaged, externally-facing applications (web, CMS, etc., eg: JBoss)
- Most of the work is done using widely available tools, as well as basic batch files and .vbs scripts (which tend to be left behind)
- The adversary obtains credentials, and then begins reconnaissance activities to identify systems
- Once credentials have been obtained (such as domain admin credentials), there is no need to look for “vulnerable” systems, because they are all vulnerable
- Reconnaissance is “noisy”; an external tool is downloaded, installed, and run
- The time between initial compromise to reconnaissance to pushing out ransomware varies, but in the cases we’ve seen, it’s several months
- This means that with proper instrumentation and monitoring, this illicit activity could have been caught early, and the ransom obviated
- The ransom notification included in the infection states 1.5 bitcoin to decrypt a single system, or 22 bitcoin to decrypt all systems
- The CTU worked one ransomware incident where, after the victim initiated communication with the adversary, the ransom demanded was raised to 40 bitcoins for all systems, as opposed to 22 bitcoins.