Tenable Network Security, Inc., a global leader in cybersecurity, today announced the latest release of its cloud-based Tenable.io platform, making it the industry’s first vulnerability platform to incorporate and unify IT and OT security across the full range of traditional and modern assets.
The demands of security platforms have grown and couple that with the computing and software developments, the need for a platform that delivers results by adopting a new set of dynamic IT assets, including cloud, microservices and containers is a god-send for those in the IT security industry. This new tool allows organisations to manage their security programs and address their exposures and risks in an agile and strategic way.
“Massive shifts in computing have left enterprises struggling to gain visibility into their exposure areas. The rise of IoT and the convergence of IT and OT are only compounding the issue,” said Dave Cole, chief product officer at Tenable. “The vulnerability management tools of yesterday are falling short in providing CISOs with a complete and reliable view of the entire modern attack surface so they can take a proactive approach to managing the security challenges of today and tomorrow.”
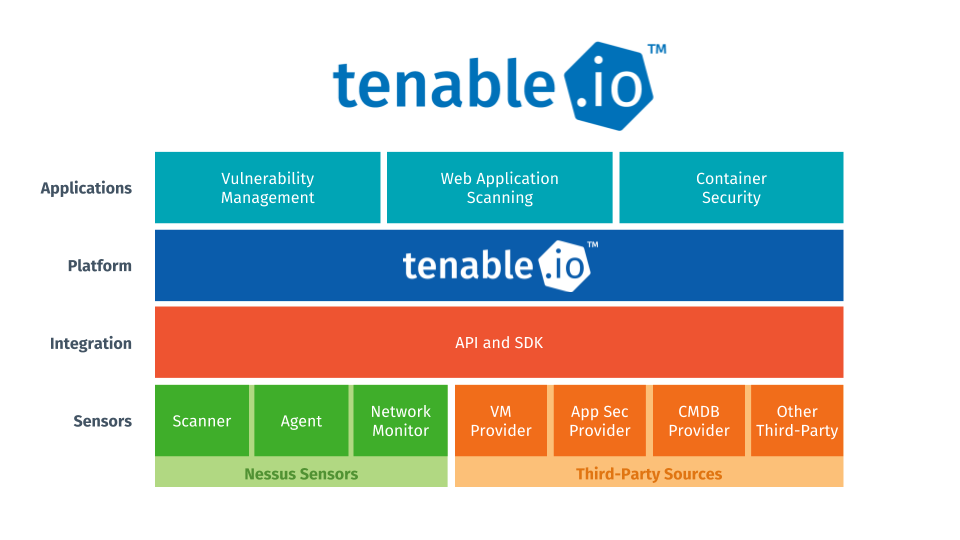
Main features of the Tenable.io Platform:
- General Availability of Tenable.io Container Security – Tenable.io Container Security seamlessly and securely enables DevOps processes by providing visibility into the security of container images as they are created. Through integration with the container build process, it provides vulnerability assessment, malware detection and policy enforcement prior to container deployment — enabling security teams to turn a blind spot into a strength.
- Nessus Network Monitor Support for IT, OT and IoT Assets – Nessus Network Monitor (formerly Passive Vulnerability Scanner or PVS) passively analyzes network traffic to provide continuous visibility into managed and unmanaged assets on the network, including IT, OT and IoT assets. It includes new capabilities for asset discovery and vulnerability identification on critical infrastructure and embedded systems, such as ICS and SCADA systems, which require a non-intrusive approach to vulnerability management. Nessus Network Monitor provides coverage for operational technologies in a variety of safety-critical infrastructure industries, including oil and gas, energy, utilities, public infrastructure, manufacturing, and medical/healthcare. Supported protocols include Bacnet, CIP, DNP3, Ethernet/IP, Modbus/TCP, Siemens S7, ICCP, IEC 60870-5-104, IEEE C37.118, OpenSCADA, and more.
- Shadow Brokers, WannaCry and Intel AMT Scan Policy Templates – Tenable.io includes pre-built scan templates for identifying systems exposed to all Shadow Brokers exploits, including WannaCry, EternalRocks and any new versions of these attacks, as well as a check for the recent Intel AMT vulnerability (INTEL-SA-00075). Take control of your network and protect against these and future threats with a free 60-day trial of Tenable.io Vulnerability Management at https://www.tenable.com/products/tenable-io/vulnerability-management/evaluate.
- Tenable.io Web Application Scanning – Tenable.io Web Application Scanning, a new product within the Tenable.io platform that safely and automatically scans web applications to accurately identify vulnerabilities, will be generally available on July 14, 2017. To learn more, visit tenable.com/products/tenable-io/web-application-scanning.
The rapid pace of innovation has created a rapidly changing attack surface, with DevOps teams in the driver’s seat and security as an afterthought. On the other end of the spectrum are Operational Technology (OT) assets, including industrial control systems (ICS) and supervisory control and data acquisition (SCADA). These safety-critical systems were designed for precision and reliability, not built with security in mind.
OT assets, coupled with the rise of the internet of things (IoT) where everything from pacemakers to automobiles are now connected devices, have exploded the attack surface to a point beyond control. Organizations need a way to discover all of these assets and manage vulnerabilities holistically, yet have been forced to use legacy scanning and agent-based tools designed for the world of traditional IT. These old approaches do not fit in the modern world of IT, or the world of OT and IoT where a non-intrusive approach to asset discovery and vulnerability detection is required.








