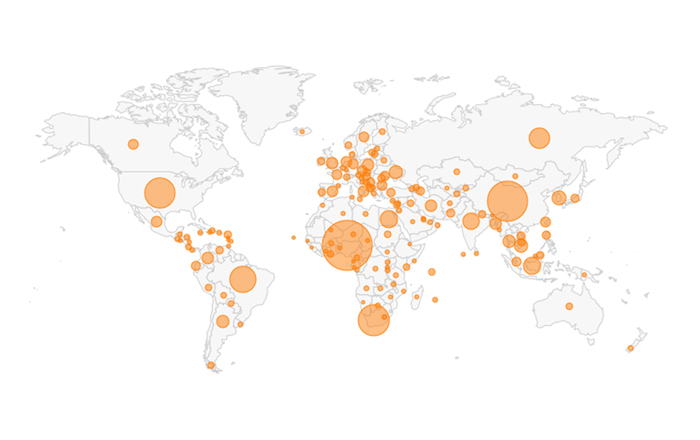
Proofpoint, Inc., a leading cybersecurity and compliance company, today released its Cloud Application Attack Snapshot: Q1 2019 research, which examined over one hundred thousand cloud application attacks aimed at global organizations between September 2018 and February 2019. Overall, targeting attempts increased by 65 percent during that time period with 40 percent originating in Nigeria. China was the second most prevalent country of origin, with 26 percent of attacks originating from Chinese IP addresses.
Cloud application attacks use intelligence driven brute-force techniques (to crack passwords) and sophisticated phishing methods to lure victims into clicking and revealing their authentication credentials to break into cloud applications including Microsoft Office 365 and Google G Suite. If successful, attackers often increase their foothold in organizations by spreading laterally through internal phishing messages to infect additional users, access confidential information, and fraudulently route funds.
“As organizations continue to move their mission-critical business functions to the cloud, cybercriminals are taking advantage of legacy protocols that leave individuals vulnerable when using cloud applications,” said Ryan Kalember, executive vice president of Cybersecurity Strategy for Proofpoint. “These attacks are laser-focused on specific individuals, rather than infrastructure, and continue to grow in sophistication and scope. As a best practice, we recommend that organizations establish a cloud-first approach to security that prioritizes protecting employees and educates users to identify and report these advanced techniques and methods.”
Proofpoint found that the education sector was the most targeted of both brute-force and sophisticated phishing attempts. This industry, and students especially, are highly vulnerable due to their remote nature.
Additional Proofpoint Cloud Application Attack Research Findings
Brute-Force Cloud App Attack Findings:
· IMAP-based password spraying attacks are the most popular and extensive technique used to compromise Microsoft Office 365 accounts. These attacks occur when cybercriminals attempt common or recently leaked credentials across many different accounts at the same time.
· Most brute-force attacks originated in China (53%), followed by Brazil (39 percent), and the U.S. (31 percent).
· Over 25 percent of examined Office 365 tenants experienced unauthorized logins and over 60 percent were actively targeted. Overall, the success ratio in Q1 2019 was 44 percent.
Phishing Cloud App Attack Findings:
· Most phishing cloud app attacks originate from Nigeria (63 percent), followed by South Africa (21 percent), and the United States via VPNs (11 percent).
· Attackers will often modify email forwarding rules or set email delegations to maintain access. They will also use conspicuous VPN services to bypass conditional access and geolocation-based authentication.
To access Proofpoint’s Cloud Application Attack Snapshot: Q1 2019 research, please visit: https://www.proofpoint.com/us/threat-insight/post/threat-actors-leverage-credential-dumps-phishing-and-legacy-email-protocols