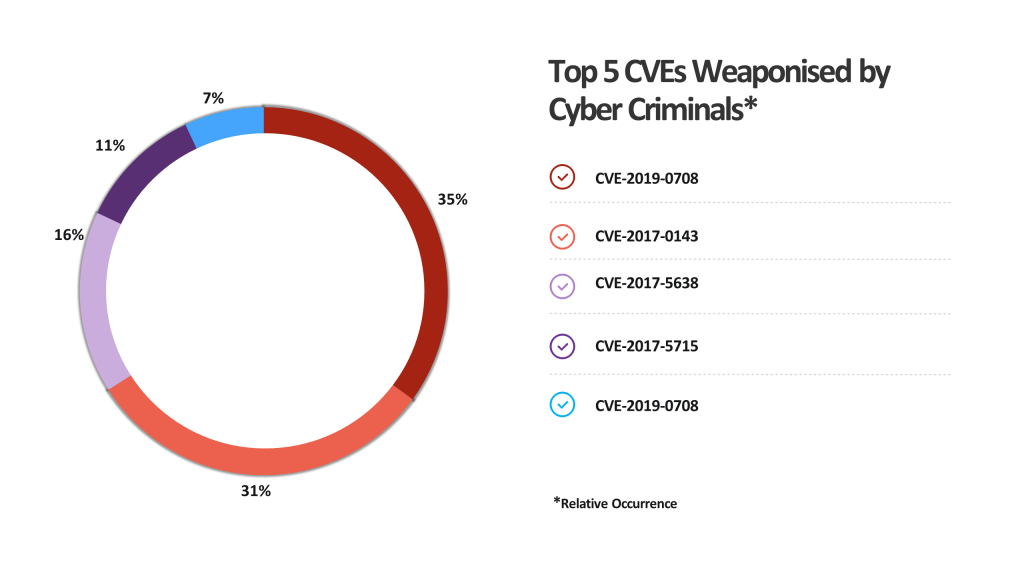
Every year, fullstack vulnerability management provider Edgescan releases its Vulnerability Statistics Report, which highlights the highest impact vulnerabilities still out there in the wild. As a teaser to their 2021 report, their team has compiled a useful list of the top 5 known, unpatched vulnerabilities leveraged by cybercriminals in order launch attacks on unsuspecting organisations.
The list includes the CVE, its impact and the threat actors taking advantage of the vulnerabilities.
| 1. CVE-2019-0708 - Often known as the BlueKeep |
| CVSS 2 Score |
| 10 |
| Impacted Systems |
| Microsoft Windows |
| Description |
| A remote code execution vulnerability exists in Remote Desktop Services formerly known as Terminal Services when an unauthenticated attacker connects to the target system using RDP and sends specially crafted requests, aka ‘Remote Desktop Services Remote Code Execution Vulnerability’. |
| Impact |
| Someone can use Remote Desktop feature of Windows to login onto your pc and take control. There is total information disclosure, resulting in all system files being revealed |
| Threat Actor |
| Kelvin SecTeam (Venezuela, Colombia, Peru) |
| Reference Link |
| CVE-2019-0708 : A remote code execution vulnerability exists in Remote Desktop Services formerly known as Terminal Services when an unau (cvedetails.com) |
| 2. CVE-2017-0143 - DOUBLEPULSAR Payload use this CVE |
| CVSS 2 Score |
| 9.3 |
| Impacted Systems |
| Microsoft SMB |
| Description |
| The SMBv1 server in Microsoft Windows Vista SP2; Windows Server 2008 SP2 and R2 SP1; Windows 7 SP1; Windows 8.1; Windows Server 2012 Gold and R2; Windows RT 8.1; and Windows 10 Gold, 1511, and 1607; and Windows Server 2016 allows remote attackers to execute arbitrary code via crafted packets, aka “Windows SMB Remote Code Execution Vulnerability.” This vulnerability is different from those described in CVE-2017-0144, CVE-2017-0145, CVE-2017-0146, and CVE-2017-0148. |
| Impact |
|
| Threat Actor |
| APT3 (China), Calypso (China) |
| Reference Link |
| Windows Server Message Block Request Handling Flaws Let Remote Users Obtain Potentially Sensitive Information and Execute Arbitrary Code - SecurityTracker |
| 3. CVE-2017-5638 |
| CVSS 2 Score |
| 10 |
| Impacted Systems |
| Apache Struts |
| Description |
| The Jakarta Multipart parser in Apache Struts 2 2.3.x before 2.3.32 and 2.5.x before 2.5.10.1 has incorrect exception handling and error-message generation during file-upload attempts, which allows remote attackers to execute arbitrary commands via a crafted Content-Type, Content-Disposition, or Content-Length HTTP header, as exploited in the wild in March 2017 with a Content-Type header containing a #cmd= string. |
| Impact |
|
| Threat Actor |
| Lazarus Group (North Korea) |
| Reference Link |
| (Oracle Issues Fix for Oracle WebLogic) Apache Struts Jakarata Multipart Parser Bug Lets Remote Users Execute Arbitrary Commands on the Target System - SecurityTracker |
| 4. CVE-2017-5715 - Also known as Spectre |
| CVSS 2 Score |
| 4.7 |
| Impacted Systems |
| ARM, Intel |
| Description: |
| Systems with microprocessors utilizing speculative execution and indirect branch prediction may allow unauthorized disclosure of information to an attacker with local user access via a side-channel analysis. |
| Impact: |
| A local user can run specially crafted code to cause the CPU to speculatively execute an indirect branch to leak memory contents from another process into a CPU cache and then read the contents of the cache [CVE-2017-5715]. A local user can view arbitrary virtual memory contents on the target CPU device [which can lead to elevated privileges on the target system] |
| Threat Actor |
| Unknown |
| Reference Link |
| Intel/AMD/ARM CPU Data Cache Race Conditions Let Local Users Read Arbitrary Virtual CPU Memory - SecurityTracker |
| 5. CVE-2017-10271 - Used by CyrptoMiners |
| CVSS 2 Score |
| 5 |
| Impacted Systems |
| Oracle WebLogic Server |
| Description |
| A remote user can exploit a flaw in the Oracle WebLogic Server WLS Security component to gain elevated privileges. |
| Impact |
|
| Threat Actor |
| Rocke Gang (Chinese Cybercrime) |
| Reference Link |
| Oracle WebLogic Server Flaws Let Remote User Gain Elevated Privileges, Modify Data, and Deny Service on the Target System - SecurityTracker |
Visit the Vulnerability Statistics Resources for more information and to view the Edgescan 2020 Stats Report. Register your interest to receive one of the first copies of the 2021 Report, due in February 2021.








