Edgescan, the provider or fullstack vulnerability management, has released its Q3 Vulnerability Snapshot, a new, brief report showing the current vulnerability landscape based on thousands of assessments performed globally.
Compiled by Eoin Keary, CEO of Edgescan, the report’s findings highlight the variability when it comes to cybercriminals’ favourite vulnerabilities to exploit.
Looking at this quarterly report, we can already tell that the 2022 Vulnerability Satistics Report will highlight an every changing attack surface and once again highlight the importance of Attack Surface Management.
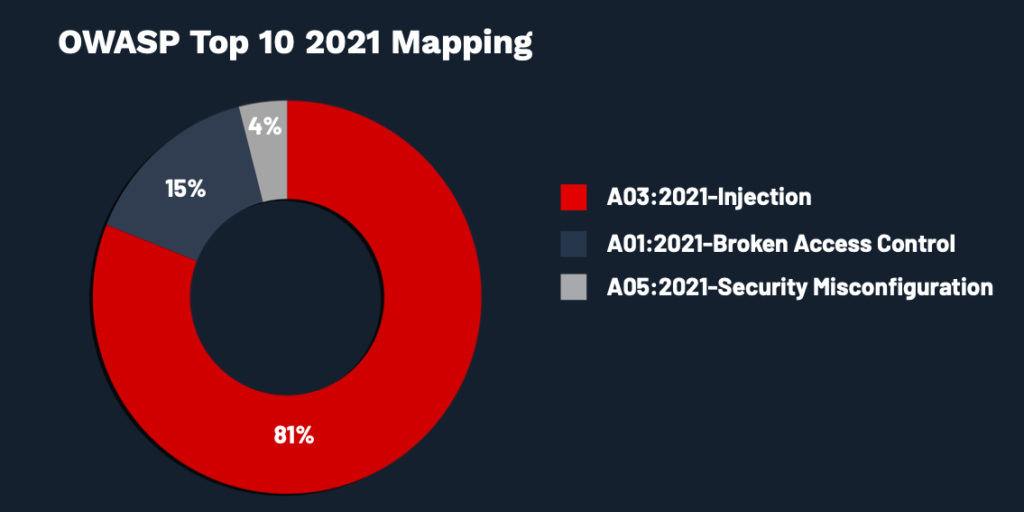
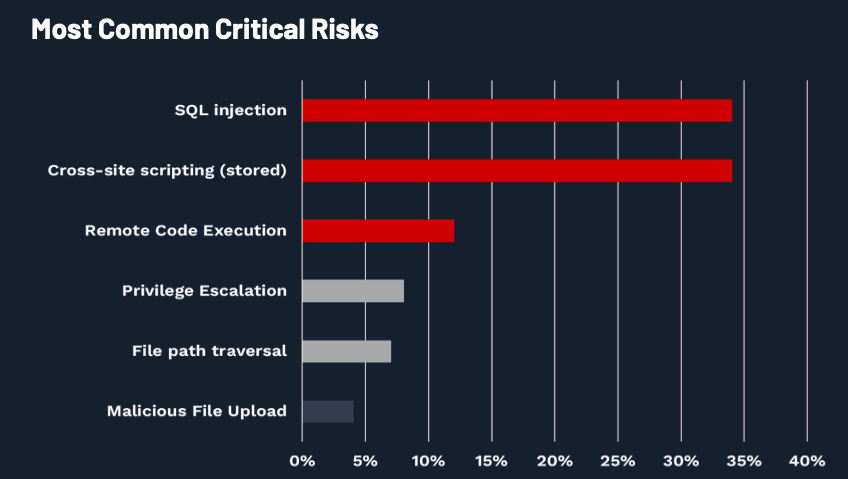
Web application critical risks
The top critical risk for Q3 is currently SQL Injection (A03:2021-Injection) which has increased from Q2 and Q1. In Q3, we have seen an increase in Cross-Site Scripting (stored) but down from Q1 (37%) showing that it’s once again showing up again.
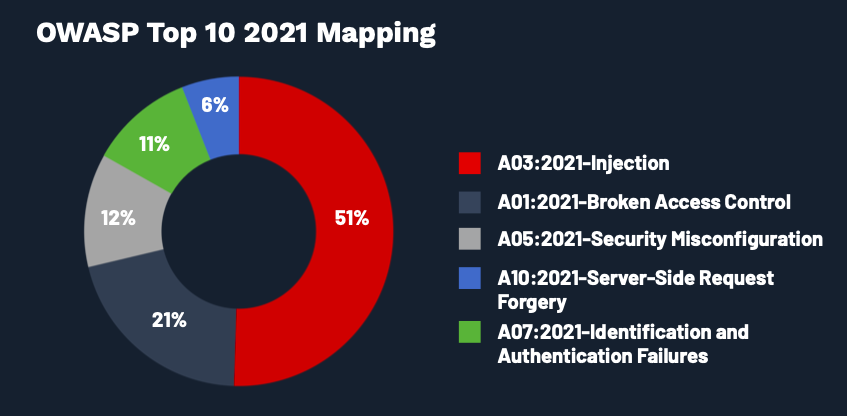
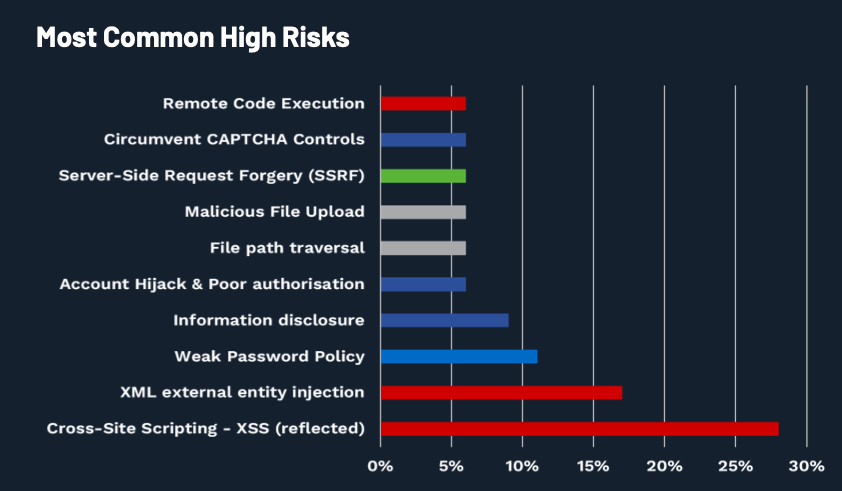
Web application high risks
The web application is currently highlighting that 51% of risks are currently falling under Injection (A03:2021-Injection) with Broken Access Control (A01:2021-Broken Access Control) following up with 21%. This can be seen with Cross-Site Scripting – XSS (Reflected) as being the number 1 cause in this quarter and last quarter.
For more information, visit: https://www.edgescan.com








