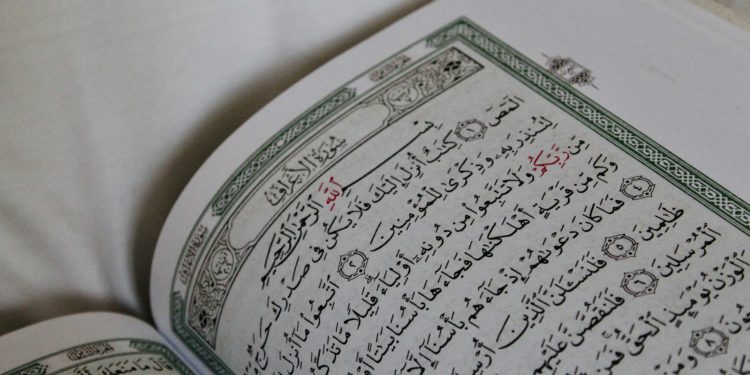
A report by Motherboard says that the US military has been mining data from the Muslim prayer app, Muslim Pro. Muslim Pro is one of the “most popular Muslim apps”, boasting over 98 million downloads. The app reminds users of their daily prayers and provides them with readings from the Quran. The app also tracks users’ locations with this data sold to brokers. One of the buyers of the app’s data is reportedly the US military, who are using that data supposedly for ‘counterterrorism’.
It is not unusually for apps to sell on their users’ location data to third-party brokers with Muslim Pro being one of the hundreds of apps to do so. The ownership of this specific data by the US military is notable as the US military has consistently targeted predominantly Muslim terror groups in the middle east for a number of years. Therefore, this news has concerned a number of privacy advocates, but the app reports that they keep the users’ data anonymised.