With results from more than 100 professionals in cybersecurity, Armis released a survey that explored the risks and struggles within the industry as the environment changes. As the landscape of cybersecurity changes rapidly, security intel being reported to companies may be constantly outdated.
According to the results, while top management in companies in the past 6 months have spent more time involved with cybersecurity concerns, almost 23% of the professionals surveyed believed that board members are not involved enough.
Respondents have also reported that many of their companies have started tightening their security protocols within the last 6 months. Still, 75% had not completed a thorough risk assessment in the same period of time. This is a big issue for security.
Andy Norton, European Cyber Risk Officer at Armis, explained, “Given how fast things evolve in most of today’s environments, six months can be an eternity.”
If risk assessments are performed over six months apart, then security professionals are providing top management with out-of-date information that could be giving threat actors a major head-start.
“Organisations can and should aim higher, particularly as capabilities now exist for performing continuous risk assessments, which can help them achieve the next crucial step towards risk assessment maturity,” he said.
Indeed, the results also pointed out that the top five priorities for cybersecurity include risk assessment as well as asset visibility, security awareness training, compliance, and threat detection and incident response, and some of the risks that companies need to be looking at are employee actions (think: accessing risky websites and applications on company networks), lack or limited asset visibility, and bad patch management practices.

This is especially important these days as 60% of respondents noted an increase in security alerts, and over half were concerned about the UK CNI (Critical National Infrastructure) and how it would hold up against potential Russian attacks.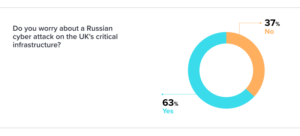
NATO countries and organisations must reinforce their defences, as vulnerabilities increase, Norton noted. This is especially important due to the lack of timely information. “There is room for improvement when it comes to providing business leaders with real-time information that will help them allocate the right resources and make the best decisions regarding their cybersecurity strategies.”
Without timely and up-to-date information, companies will struggle to keep up with the rapidly changing landscape in cybersecurity. Threat actors will always be ahead, the Armis survey suggests, unless companies fortify their security practices while targeting and remediating their vulnerabilities.








