Most successful breaches involve stolen or compromised credentials that are used to escalate privileges and move laterally across a network, something which privileged access management (PAM) offerings are ideally suited to protect against. Keeper Security, the leading provider of zero-trust and zero-knowledge cybersecurity software protecting passwords, secrets and connections, highlights S&P Market Intelligence data showing that just 43% of SMBs have deployed PAM, compared to other leading security technologies like network, email and endpoint security and SIEM tools, which are all above 75% deployment.
The study posits that traditional PAM products have typically been extremely complex, expensive to deploy and maintain as well as extremely difficult to use, while also requiring substantial dedicated staff to operate – putting them out of reach for most smaller businesses.
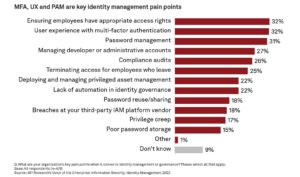
“With the expansion of the attack surface due to remote and hybrid working, privileged access management is becoming increasingly critical. At the same time, the definition of a ‘privileged user’ needs to widen to address a broader range of employees – especially in small businesses, where access rights may be more pervasive,” said Darren Guccione, CEO and co-founder at Keeper Security. “However, SMB adoption of PAM is lagging due to traditionally high barriers of entry, which is making them low hanging fruit for attackers. In order to bolster security, organizations should seek flexible, easy to use, cloud-based PAM solutions that are cost effective and offer a full stack of IAM capabilities,” he continued.
As cloud-native PAM adapts to a ‘shift left’ world, the report highlights that it must also address a wider range of resources including Infrastructure as a Service, (IaaS), Platform as a Service (PaaS), containers, Kubernetes and serverless functions, infrastructure as code, etc. Consequently, PAM must support a wider range of users, all of which have access to digital intellectual property and other confidential and sensitive company data.
Keeper Security’s own next-generation KeeperPAM solution is specifically designed for perimeterless and multi-cloud environments without prohibitive costs or deployments associated with traditional PAM solutions. It addresses the need to achieve visibility, security, reporting and control across an entire organisation, for every user, on every device, from every location.








